If you have been doing any kind of work within the federal space, or even thinking about it, you’ve probably heard the acronym “CMMC”. These four letters have been floating around in contract conversations, procurement emails, and the occasional panic-driven Google search. And if you are like most organizations trying to make sense of it, your first reaction was probably something along the lines of: “Where do I even start?“
That is a fair reaction. The Cybersecurity Maturity Model Certification program has had a long and, at times, messy road to where it is today. Understanding how it got here is actually one of the most useful ways to understand what it is, and what it is asking for organizations to do.
A Little Bit of “Chicken or the Egg”: How We Got Here
To understand CMMC, you first need to understand Controlled Unclassified Information, better known as CUI. And to understand CUI, you need to buckle up for a ride in the Wayback Machine.
For a long time, the federal government had a reasonably clear handle on classified information. There were rules, classifications, clearances, and procedures for handling anything that carried a national security label. What the government did not have was a consistent way to protect the enormous volume of sensitive but unclassified information that flows through agencies, contractors, and their partners on any given day. (Think of things such as technical specifications, export-controlled research, privacy data, or sensitive law enforcement information.) The worst part of all of it was that each agency was essentially making up its own rules, using its own labels, and calling things different names. To put it in modern terms, this would be classified as a “hot mess”.
In 2010, President Obama signed Executive Order 13556, which created a standardized framework for how agencies should identify, mark, handle, and protect this category of information. That framework formalized the term “Controlled Unclassified Information” and created the CUI Program under the National Archives and Records Administration. The idea was simple enough: if we are going to protect this stuff consistently, we need to call it the same thing and treat it the same way across the board.
So, there you have the egg.
Now for the chicken. The federal government does not operate in a vacuum. Billions of dollars’ worth of work, research, development, and services happen through contractors and subcontractors. Many of whom are small and mid-size businesses that handle CUI as part of their normal operations. If the government is going to protect CUI internally, it also needs the organizations working on its behalf to protect it too. Otherwise, you have secured the front door and left the back window wide open.
Enter NIST SP 800-171
In 2015, the National Institute of Standards and Technology published Special Publication 800-171: Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations. If CUI was the problem, NIST 800-171 was the first real answer aimed at the federal contractor community.
The publication laid out 110 security requirements across 14 control families, covering everything from access control and incident response to configuration management and system and communications protection. It was a set of requirements designed to create a genuine security baseline.
The Defense Federal Acquisition Regulation Supplement, or DFARS, made 800-171 a contractual requirement for Department of Defense contractors in 2017. If your contract involved CUI, you were expected to meet these requirements. (I need to add “In theory” to this section, because the biggest issue here was that compliance was almost entirely self-attested. Meaning that every company could look at their environment and say “Yeah, that should be good enough…”.)
Contractors submitted a score on a government portal, and that score was largely taken at face value. As you might imagine, the honor system produced some…optimistic results.
Studies and audits over the years revealed that the self-assessment scores many contractors reported had very little relationship to their actual security posture. Some organizations with high scores had significant, obvious gaps. The Department of Defense (DoD) had a requirement on paper that was not producing real-world security outcomes, and that was a problem that was not going to fix itself.
The Start of CMMC: A Noble Idea with a Rocky Launch
The Cybersecurity Maturity Model Certification (CMMC) program was introduced in 2020 as the DoD’s answer to the self-attestation problem. The premise itself was pretty straightforward: instead of allowing contractors to grade their own homework, the government would require independent third-party assessments for organizations handling the most sensitive CUI. The assessments must be conducted by accredited organizations against a defined set of practices across maturity levels.
The original CMMC 1.0 model had five maturity levels, and the rollout plan was ambitious at best. By some estimates, it was expected to apply to tens of thousands of contractors across the defense industrial base. What followed was a significant amount of industry pushback, logistical challenges, and recognition that the original program had some real design flaws right from the get-go. The assessment infrastructure was not built to handle the scale. Costs for third-party assessments were ridiculous and prohibitive for small businesses. Not to mention that the whole maturity model in itself was causing unnecessary complexity that went beyond what NIST 800-171 already required.
So, like what happens quite frequently in Government land, the DoD went back to the drawing board.
CMMC 2.0: A Streamlined Approach
In late 2021, the DoD announced CMMC 2.0, which collapsed the five-level model down to three levels and re-anchored the entire program back to NIST 800-171 as the gold standard. The entire philosophy shifted toward making the program more accessible to many, more aligned with existing requirements, and more realistic for the contractors it was meant to reach.
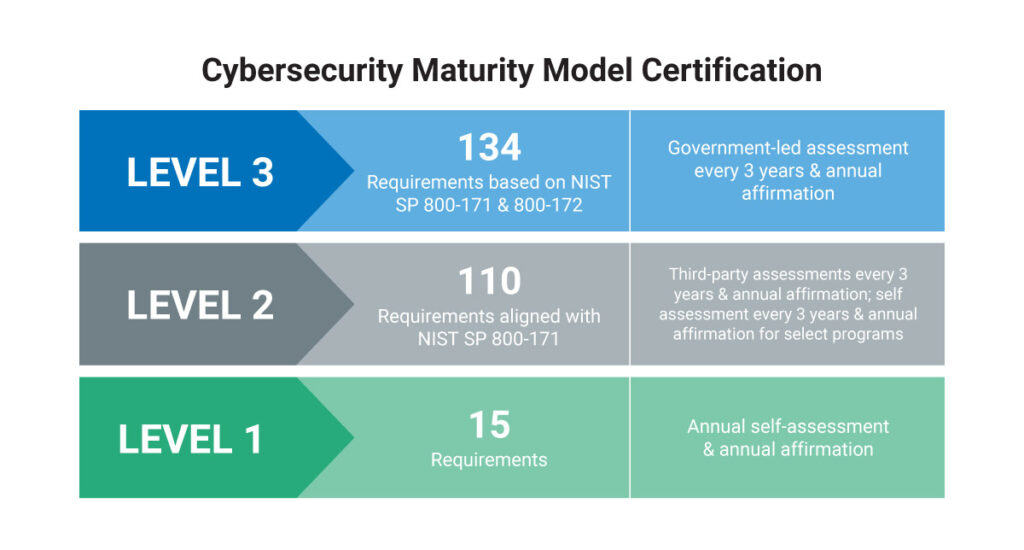
The three levels work like this. Level 1 covers basic cyber hygiene, aligns to the 15 practices in FAR 52.204-21, and allows for annual self-attestation by a senior company official. Most organizations should be doing most of these things already, so the level of effort could be small. Level 2 aligns directly to all 110 practices in NIST 800-171 and, for most contracts involving CUI, requires a third-party assessment by a Certified Third-Party Assessment Organization, known as a C3PAO.
Level 3 is very similar but is much stricter. Level 3 is reserved for the highest-priority programs and adds additional requirements from NIST SP 800-172 on top of Level 2. To make things a little tougher, all Level 3 assessments are conducted by the Defense Contract Management Agency (DCMA) through its Defense Industrial Base Cybersecurity Assessment Center, known as DIBCAC. Sorry gang, no C3PAO allowed for the highest tier.
The final CMMC rule was published in the Federal Register in late 2024 and began its phased rollout into contracts in 2025. So here we are. It is not hypothetical anymore. It is in contracts now, and it will continue to expand as we move forward.
What Most Organizations Do Not Realize
Here is where the conversation usually gets uncomfortable, and it is worth being direct about it.
Most organizations that believe they are “pretty close” to CMMC compliance are not nearly as close as they think. The self-assessment process under NIST 800-171 requires a scored assessment using the DoD Assessment Methodology, where you start at 110 points and lose points for every practice that is not fully implemented. A perfect score is 110. Many organizations that have gone through honest, rigorous assessments are sitting well below that mark, sometimes significantly.
The most common gaps we see from a consultant’s perspective are not exotic or technical. They tend to be things like:
- No formal System Security Plan documenting how each 800-171 requirement is being met.
- No documented Plan of Action and Milestones showing how identified gaps are being addressed.
- MFA that exists for some users but not all (and CMMC requires all).
- Access control practices that work well operationally but have never been formally documented and tested.
I have to be 100% honest here: The documentation requirements for CMMC are a grind. Writing policies, procedures, and a system security plan for your organization is time consuming and not for the faint of heart. We must remember that the documentation part of this complex puzzle matters just as much as the technical controls.
There is also a subcontractor piece that catches people off guard. If you flow CUI down to subs, your compliance obligation follows it. Your security posture is only as strong as the weakest link in your supply chain, and the DoD knows it. Before hitching your wagon with another downstream partner, it is important to make sure that organization is security minded and thinking on the same level.
CMMC is a Marathon, Not a Sprint
This is possibly the most important thing to take away from this entire article. Organizations that approach CMMC as a project with a start date and an end date tend to struggle. Organizations that approach it as a program, something you build deliberately over time and sustain, tend to do much better. You have to have the stamina to make it to the finish line.
A realistic CMMC Level 2 readiness effort for an organization that is starting from a modest baseline can take anywhere from 12 to 24 months depending on the size of the environment, the number of gaps that exist, the available internal resources, and how quickly decisions can be made and funding can be allocated. That timeline is not meant to discourage anyone. It is meant to make the case for starting now rather than waiting until a contract requires it.
There are real costs involved. Those costs include the assessment itself, any remediation work to close gaps before the assessment, the ongoing maintenance of policies and procedures, and potentially changes to your infrastructure or access environment. It doesn’t happen overnight, and it shouldn’t be attempted without a plan.
Where Arctic IT Can Help
We work with organizations that depend on federal, defense, and tribal contracts. We understand that CMMC can feel like a lot of noise and very little signal when you are trying to figure out what it all means for your business. So, we built a practical starting point.
Arctic IT’s 1-Hour CMMC Consultation is a focused working session with our cybersecurity consultants who are experienced in both CMMC and NIST 800-171. In this session, we discuss your business, your contracts, and your current security posture. We help you determine whether CMMC applies to you and at what level. We take an honest look at your existing security and documentation practices, and we assess your incident response readiness.
After the session, you receive a written CMMC Action Plan tailored to your organization. It will tell you where you stand in plain language, what your key gaps and risks are, what remediation steps you should prioritize, and what it will realistically take in time, money, and effort to move toward your target level. No jargon-heavy report that collects dust. A real plan you can actually use.
CMMC does not have to be paralyzing. With the right guidance, the path forward becomes a lot clearer.
Ready to turn CMMC confusion into a clear plan? That is exactly what we are here for. Connect with us today to get started with your CMMC Consultation and Action Plan.
Run with us.

By Kevin Fassanella, Director of Security and Compliance at Arctic IT

