Join leaders from Chehalis Tribal Enterprises and Arctic IT for a conversation designed to help tribal leaders and business executives understand...
Blog
ResourcesNews, Articles and Events
Extending Dynamics 365 Finance Functionality with Microsoft Teams
If you use Dynamics 365 Finance and Supply Chain Management (D365 F&SCM) daily, chances are you’re also using Microsoft Teams throughout your...
Microsoft Sentinel: Why Security Teams Need a SIEM to Strengthen Threat Detection and Response
Security leaders are facing a new reality. The “perimeter” is gone, identities are the new control plane, and attackers move faster than most teams...
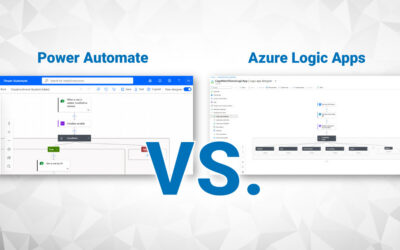
Power Automate vs. Azure Logic Apps: How to Choose the Right Automation Tool
Everyone agrees automation is a good idea, but the challenge is choosing the right tool. On paper, automation promises faster processes, fewer...
The Role of Microsoft Entra ID in Identity and Access Management
Microsoft Entra ID is a cloud-based identity and access management (IAM) service that plays a crucial role in securing user authentication and...
A Developer’s Dive into Custom Connectors for Power Platform and Azure Logic Apps
Most people don’t realize it, but the only thing standing between you and the automation your business really needs is…you. Not Microsoft. Not a...
How to Effectively Manage Security in Dataverse for Business Units and Teams
When organizations begin working with Microsoft Dataverse, one of the first challenges they encounter is managing security. Questions around who can...
2026 Tribal IT Budgeting: Why Cybersecurity, AI, and Policy are Non-Negotiable
In 2026, the question isn’t whether tribal governments will face cyber threats – it’s whether they’ll be prepared. That was the core message...